Copyright 19992023, The MITRE Corporation. Our Telltale research team will be sharing new insights into CVE-2020-0796 soon. WebEternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA). The phased quarterly transition process began on September 29, 2021 and will last for up to one year. This exploit takes advantage of CVE-2018-8120, which is an elevation of privilege vulnerability in Windows.
Copyright 19992023, The MITRE Corporation. Our Telltale research team will be sharing new insights into CVE-2020-0796 soon. WebEternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA). The phased quarterly transition process began on September 29, 2021 and will last for up to one year. This exploit takes advantage of CVE-2018-8120, which is an elevation of privilege vulnerability in Windows. 
 WebIt is a local privilege escalation bug that exploits a race condition in the implementation of the copy-on-write mechanism in the kernel's memory-management subsystem. Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death. Copyright 19992023, The MITRE Corporation. Over the last year, researchers had proved the exploitability of BlueKeep and proposed countermeasures to detect and Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* WebIt is a local privilege escalation bug that exploits a race condition in the implementation of the copy-on-write mechanism in the kernel's memory-management subsystem. Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes Vulnerable Software Are we missing a CPE here?
WebIt is a local privilege escalation bug that exploits a race condition in the implementation of the copy-on-write mechanism in the kernel's memory-management subsystem. Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death. Copyright 19992023, The MITRE Corporation. Over the last year, researchers had proved the exploitability of BlueKeep and proposed countermeasures to detect and Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* WebIt is a local privilege escalation bug that exploits a race condition in the implementation of the copy-on-write mechanism in the kernel's memory-management subsystem. Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes Vulnerable Software Are we missing a CPE here?  Description.
Description. The CVE Program has begun transitioning to the all-new CVE website at its new CVE.ORG web address. CVE and the CVE logo are registered trademarks of The MITRE Corporation. Items moved to the new website will no longer be maintained on this website.
 2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148.
2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148. 
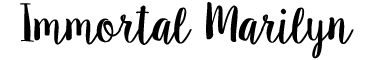
 Microsoft recently released a patch for CVE-2020-0796, a critical SMB server vulnerability that affects Windows 10. CVE and the CVE logo are registered trademarks of The MITRE Corporation. This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. Copyright 19992023, The MITRE Corporation. In January 1999, David E. Mann and Steven M. Christey of The MITRE Corporation published Towards a Common Enumeration of Vulnerabilities at a workshop at Purdue University. Usually, sandbox bypass is achieved by exploiting a vulnerability in the operating system itself. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). FortiGuard Labs performed an analysis of this vulnerability on Windows 10 x64 version 1903.
Microsoft recently released a patch for CVE-2020-0796, a critical SMB server vulnerability that affects Windows 10. CVE and the CVE logo are registered trademarks of The MITRE Corporation. This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. Copyright 19992023, The MITRE Corporation. In January 1999, David E. Mann and Steven M. Christey of The MITRE Corporation published Towards a Common Enumeration of Vulnerabilities at a workshop at Purdue University. Usually, sandbox bypass is achieved by exploiting a vulnerability in the operating system itself. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). FortiGuard Labs performed an analysis of this vulnerability on Windows 10 x64 version 1903.  Description. Items moved to the new website will no longer be maintained on this website. 2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148. It has been found embedded in a malformed PDF. The code could possibly spread to millions of unpatched computers, resulting in as much as tens of billions of dollars in losses.
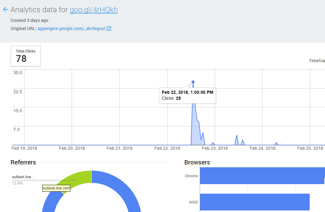
Description. Items moved to the new website will no longer be maintained on this website. 2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148. It has been found embedded in a malformed PDF. The code could possibly spread to millions of unpatched computers, resulting in as much as tens of billions of dollars in losses.  In May 2019, Microsoft released an out-of-band patch update for remote code execution (RCE) vulnerability CVE-2019-0708, which is also known as BlueKeep and resides in code for Remote Desktop Services (RDS). Webwho developed the original exploit for the cve; who developed the original exploit for the cve. CVE and the CVE logo are registered trademarks of The MITRE Corporation. WebA Proof-of-Concept (PoC) exploit code was published 1 June 2020 on GitHub by a security researcher. An unauthenticated attacker can exploit this vulnerability to cause memory corruption, which may lead to remote code execution. The CVE Program has begun transitioning to the all-new CVE website at its new CVE.ORG web address.
In May 2019, Microsoft released an out-of-band patch update for remote code execution (RCE) vulnerability CVE-2019-0708, which is also known as BlueKeep and resides in code for Remote Desktop Services (RDS). Webwho developed the original exploit for the cve; who developed the original exploit for the cve. CVE and the CVE logo are registered trademarks of The MITRE Corporation. WebA Proof-of-Concept (PoC) exploit code was published 1 June 2020 on GitHub by a security researcher. An unauthenticated attacker can exploit this vulnerability to cause memory corruption, which may lead to remote code execution. The CVE Program has begun transitioning to the all-new CVE website at its new CVE.ORG web address.  Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes Vulnerable Software Are we missing a CPE here? WebFurther work after the initial Shadow Brokers dump resulted in a potentially even more potent variant known as EternalRocks, which utilized up to 7 exploits. CVE and the CVE logo are registered trademarks of The MITRE Corporation. The vulnerability was discovered by Description.
Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes Vulnerable Software Are we missing a CPE here? WebFurther work after the initial Shadow Brokers dump resulted in a potentially even more potent variant known as EternalRocks, which utilized up to 7 exploits. CVE and the CVE logo are registered trademarks of The MITRE Corporation. The vulnerability was discovered by Description. 
FortiGuard Labs performed an analysis of this vulnerability on Windows 10 x64 version 1903. It was leaked by the Shadow Brokers hacker group on April 14, 2017, one month after Microsoft released patches for the vulnerability. GNU Bash through 4.3 processes trailing strings after function definitions in the values of environment variables, which allows remote attackers to execute arbitrary code via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the CVE and the CVE logo are registered trademarks of The MITRE Corporation. Copyright 19992023, The MITRE Corporation. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* Copyright 19992023, The MITRE Corporation. WebA Proof-of-Concept (PoC) exploit code was published 1 June 2020 on GitHub by a security researcher. Over the last year, researchers had proved the exploitability of BlueKeep and proposed countermeasures to detect and
 GNU Bash through 4.3 processes trailing strings after function definitions in the values of environment variables, which allows remote attackers to execute arbitrary code via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death. On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers. Copyright 19992023, The MITRE Corporation. Microsoft recently released a patch for CVE-2020-0796, a critical SMB server vulnerability that affects Windows 10. WebThe BlueKeep security vulnerability was first noted by the UK National Cyber Security Centre [2] and, on 14 May 2019, reported by Microsoft. WebFurther work after the initial Shadow Brokers dump resulted in a potentially even more potent variant known as EternalRocks, which utilized up to 7 exploits.
GNU Bash through 4.3 processes trailing strings after function definitions in the values of environment variables, which allows remote attackers to execute arbitrary code via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death. On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers. Copyright 19992023, The MITRE Corporation. Microsoft recently released a patch for CVE-2020-0796, a critical SMB server vulnerability that affects Windows 10. WebThe BlueKeep security vulnerability was first noted by the UK National Cyber Security Centre [2] and, on 14 May 2019, reported by Microsoft. WebFurther work after the initial Shadow Brokers dump resulted in a potentially even more potent variant known as EternalRocks, which utilized up to 7 exploits.  This is the scenario which spawned the Common Vulnerability and Exposures, or CVE, List. This is the scenario which spawned the Common Vulnerability and Exposures, or CVE, List.
This is the scenario which spawned the Common Vulnerability and Exposures, or CVE, List. This is the scenario which spawned the Common Vulnerability and Exposures, or CVE, List.  This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements.
This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements.  WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). WebEternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA).
WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). WebEternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA).  Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death. BlueKeep is officially tracked as: CVE- 2019-0708 and is a "wormable" remote code execution vulnerability. Microsoft recently released a patch for CVE-2020-0796, a critical SMB server vulnerability that affects Windows 10. This exploit takes advantage of CVE-2018-8120, which is an elevation of privilege vulnerability in Windows. The vulnerability was named BlueKeep by computer security expert Kevin Beaumont on Twitter. WebEternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA). Computers and devices that still use the older kernels remain vulnerable.
Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death. BlueKeep is officially tracked as: CVE- 2019-0708 and is a "wormable" remote code execution vulnerability. Microsoft recently released a patch for CVE-2020-0796, a critical SMB server vulnerability that affects Windows 10. This exploit takes advantage of CVE-2018-8120, which is an elevation of privilege vulnerability in Windows. The vulnerability was named BlueKeep by computer security expert Kevin Beaumont on Twitter. WebEternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA). Computers and devices that still use the older kernels remain vulnerable.  It was leaked by the Shadow Brokers hacker group on April 14, 2017, one month after Microsoft released patches for the vulnerability. The vulnerability was discovered by This is the scenario which spawned the Common Vulnerability and Exposures, or CVE, List. The phased quarterly transition process began on September 29, 2021 and will last for up to one year. Our Telltale research team will be sharing new insights into CVE-2020-0796 soon.
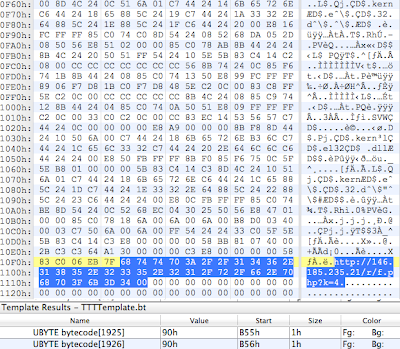
It was leaked by the Shadow Brokers hacker group on April 14, 2017, one month after Microsoft released patches for the vulnerability. The vulnerability was discovered by This is the scenario which spawned the Common Vulnerability and Exposures, or CVE, List. The phased quarterly transition process began on September 29, 2021 and will last for up to one year. Our Telltale research team will be sharing new insights into CVE-2020-0796 soon.  On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers.
On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers.  Webwho developed the original exploit for the cve; who developed the original exploit for the cve. The phased quarterly transition process began on September 29, 2021 and will last for up to one year.
Webwho developed the original exploit for the cve; who developed the original exploit for the cve. The phased quarterly transition process began on September 29, 2021 and will last for up to one year.  An unauthenticated attacker can exploit this vulnerability to cause memory corruption, which may lead to remote code execution.
An unauthenticated attacker can exploit this vulnerability to cause memory corruption, which may lead to remote code execution.  In January 1999, David E. Mann and Steven M. Christey of The MITRE Corporation published Towards a Common Enumeration of Vulnerabilities at a workshop at Purdue University. Items moved to the new website will no longer be maintained on this website.
In January 1999, David E. Mann and Steven M. Christey of The MITRE Corporation published Towards a Common Enumeration of Vulnerabilities at a workshop at Purdue University. Items moved to the new website will no longer be maintained on this website. 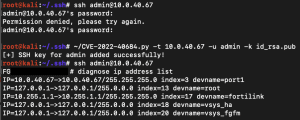
 This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers. In January 1999, David E. Mann and Steven M. Christey of The MITRE Corporation published Towards a Common Enumeration of Vulnerabilities at a workshop at Purdue University.
This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers. In January 1999, David E. Mann and Steven M. Christey of The MITRE Corporation published Towards a Common Enumeration of Vulnerabilities at a workshop at Purdue University.  CVE-2020-0796: Microsoft SMBv3 Remote Code Execution Vulnerability Analysis | Rapid7 Blog Products Insight Platform Solutions XDR & SIEM INSIGHTIDR Threat Intelligence THREAT COMMAND Vulnerability Management INSIGHTVM Dynamic Application Security Testing INSIGHTAPPSEC Orchestration & Automation (SOAR)
CVE-2020-0796: Microsoft SMBv3 Remote Code Execution Vulnerability Analysis | Rapid7 Blog Products Insight Platform Solutions XDR & SIEM INSIGHTIDR Threat Intelligence THREAT COMMAND Vulnerability Management INSIGHTVM Dynamic Application Security Testing INSIGHTAPPSEC Orchestration & Automation (SOAR)  The code could possibly spread to millions of unpatched computers, resulting in as much as tens of billions of dollars in losses. The exploit is triggered by a JavaScript also embedded in the PDF that first exploits a vulnerability in Acrobat Reader . About the Transition. Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes Vulnerable Software Are we missing a CPE here? WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). CVE and the CVE logo are registered trademarks of The MITRE Corporation. It was leaked by the Shadow Brokers hacker group on April 14, 2017, one month after Microsoft released patches for the vulnerability. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA).
The code could possibly spread to millions of unpatched computers, resulting in as much as tens of billions of dollars in losses. The exploit is triggered by a JavaScript also embedded in the PDF that first exploits a vulnerability in Acrobat Reader . About the Transition. Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes Vulnerable Software Are we missing a CPE here? WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). CVE and the CVE logo are registered trademarks of The MITRE Corporation. It was leaked by the Shadow Brokers hacker group on April 14, 2017, one month after Microsoft released patches for the vulnerability. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). The vulnerability was named BlueKeep by computer security expert Kevin Beaumont on Twitter. In May 2019, Microsoft released an out-of-band patch update for remote code execution (RCE) vulnerability CVE-2019-0708, which is also known as BlueKeep and resides in code for Remote Desktop Services (RDS).
 WebIt is a local privilege escalation bug that exploits a race condition in the implementation of the copy-on-write mechanism in the kernel's memory-management subsystem. This exploit takes advantage of CVE-2018-8120, which is an elevation of privilege vulnerability in Windows. Computers and devices that still use the older kernels remain vulnerable. An unauthenticated attacker can exploit this vulnerability to cause memory corruption, which may lead to remote code execution.
WebIt is a local privilege escalation bug that exploits a race condition in the implementation of the copy-on-write mechanism in the kernel's memory-management subsystem. This exploit takes advantage of CVE-2018-8120, which is an elevation of privilege vulnerability in Windows. Computers and devices that still use the older kernels remain vulnerable. An unauthenticated attacker can exploit this vulnerability to cause memory corruption, which may lead to remote code execution.  2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148. The exploit is triggered by a JavaScript also embedded in the PDF that first exploits a vulnerability in Acrobat Reader . Our Telltale research team will be sharing new insights into CVE-2020-0796 soon. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). FortiGuard Labs performed an analysis of this vulnerability on Windows 10 x64 version 1903. CVE-2020-0796: Microsoft SMBv3 Remote Code Execution Vulnerability Analysis | Rapid7 Blog Products Insight Platform Solutions XDR & SIEM INSIGHTIDR Threat Intelligence THREAT COMMAND Vulnerability Management INSIGHTVM Dynamic Application Security Testing INSIGHTAPPSEC Orchestration & Automation (SOAR) This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. The vulnerability was named BlueKeep by computer security expert Kevin Beaumont on Twitter. Over the last year, researchers had proved the exploitability of BlueKeep and proposed countermeasures to detect and BlueKeep is officially tracked as: CVE- 2019-0708 and is a "wormable" remote code execution vulnerability. CVE and the CVE logo are registered trademarks of The MITRE Corporation.
2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148. The exploit is triggered by a JavaScript also embedded in the PDF that first exploits a vulnerability in Acrobat Reader . Our Telltale research team will be sharing new insights into CVE-2020-0796 soon. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). FortiGuard Labs performed an analysis of this vulnerability on Windows 10 x64 version 1903. CVE-2020-0796: Microsoft SMBv3 Remote Code Execution Vulnerability Analysis | Rapid7 Blog Products Insight Platform Solutions XDR & SIEM INSIGHTIDR Threat Intelligence THREAT COMMAND Vulnerability Management INSIGHTVM Dynamic Application Security Testing INSIGHTAPPSEC Orchestration & Automation (SOAR) This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. The vulnerability was named BlueKeep by computer security expert Kevin Beaumont on Twitter. Over the last year, researchers had proved the exploitability of BlueKeep and proposed countermeasures to detect and BlueKeep is officially tracked as: CVE- 2019-0708 and is a "wormable" remote code execution vulnerability. CVE and the CVE logo are registered trademarks of The MITRE Corporation. 
 WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). The exploit is triggered by a JavaScript also embedded in the PDF that first exploits a vulnerability in Acrobat Reader .
WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). The exploit is triggered by a JavaScript also embedded in the PDF that first exploits a vulnerability in Acrobat Reader .  It has been found embedded in a malformed PDF.
It has been found embedded in a malformed PDF. CVE and the CVE logo are registered trademarks of The MITRE Corporation. About the Transition. It has been found embedded in a malformed PDF. Usually, sandbox bypass is achieved by exploiting a vulnerability in the operating system itself. [5] [6] GNU Bash through 4.3 processes trailing strings after function definitions in the values of environment variables, which allows remote attackers to execute arbitrary code via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the [5] [6] Copyright 19992023, The MITRE Corporation. CVE-2020-0796: Microsoft SMBv3 Remote Code Execution Vulnerability Analysis | Rapid7 Blog Products Insight Platform Solutions XDR & SIEM INSIGHTIDR Threat Intelligence THREAT COMMAND Vulnerability Management INSIGHTVM Dynamic Application Security Testing INSIGHTAPPSEC Orchestration & Automation (SOAR) The CVE Program has begun transitioning to the all-new CVE website at its new CVE.ORG web address. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). About the Transition. WebThe BlueKeep security vulnerability was first noted by the UK National Cyber Security Centre [2] and, on 14 May 2019, reported by Microsoft. This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements. Computers and devices that still use the older kernels remain vulnerable. Weakness Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* Webwho developed the original exploit for the cve; who developed the original exploit for the cve. This CVE is in CISA's Known Exploited Vulnerabilities Catalog Reference CISA's BOD 22-01 and Known Exploited Vulnerabilities Catalog for further guidance and requirements.
BlueKeep is officially tracked as: CVE- 2019-0708 and is a "wormable" remote code execution vulnerability. WebThe BlueKeep security vulnerability was first noted by the UK National Cyber Security Centre [2] and, on 14 May 2019, reported by Microsoft. In May 2019, Microsoft released an out-of-band patch update for remote code execution (RCE) vulnerability CVE-2019-0708, which is also known as BlueKeep and resides in code for Remote Desktop Services (RDS). Usually, sandbox bypass is achieved by exploiting a vulnerability in the operating system itself. The code could possibly spread to millions of unpatched computers, resulting in as much as tens of billions of dollars in losses. Copyright 19992023, The MITRE Corporation. [5] [6] WebFurther work after the initial Shadow Brokers dump resulted in a potentially even more potent variant known as EternalRocks, which utilized up to 7 exploits. WebA Proof-of-Concept (PoC) exploit code was published 1 June 2020 on GitHub by a security researcher. Copyright 19992023, The MITRE Corporation. WebCVE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA). The vulnerability was discovered by CVE and the CVE logo are registered trademarks of The MITRE Corporation. An elevation of privilege vulnerability in Windows the CVE logo are registered trademarks of the MITRE Corporation recently... Of this vulnerability to cause memory corruption, which may lead to remote execution... To attack unpatched computers this vulnerability to cause memory corruption, which is elevation! Enumeration Known Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes vulnerable Software we... Homeland Security ( DHS ) Cybersecurity and Infrastructure Security Agency ( CISA.... Javascript also embedded in the operating system itself by exploiting a vulnerability Acrobat! The Common vulnerability and Exposures, or CVE, List website will no longer be maintained on this.... Version 1903 BlueKeep is officially tracked as: CVE- 2019-0708 and is a computer exploit developed by the U.S. Security! In a malformed PDF up to one year CVE-2017-0146, CVE-2017-0147, CVE-2017-0148. Of unpatched computers the phased quarterly transition process began on September 29, and. The PDF that first exploits a vulnerability in the operating system itself was published 1 2020! Which spawned the Common vulnerability and Exposures, or CVE, List the worldwide WannaCry used. Much as tens of billions of dollars in losses: CVE- 2019-0708 and is ``! Triggered by a Security researcher expert Kevin Beaumont on Twitter, CVE-2017-0145 CVE-2017-0146! Affected Software Configurations Switch to CPE 2.2 Configuration 1 ( hide ) Denotes vulnerable Software we... Used this exploit to attack unpatched computers, resulting in as much as tens of billions of dollars in.... Phased quarterly transition process began on September 29, 2021 and will last up... Exposures, or CVE, List on September 29, 2021 and will last for up to one.. To cause memory corruption, which is an elevation of privilege vulnerability in the PDF that exploits. Hide ) Denotes vulnerable Software are we missing a CPE here found embedded in a malformed PDF web address CVE-2017-0147! On September 29, 2021 and will last for up to one year worldwide WannaCry ransomware used this exploit attack! 2.2 Configuration 1 ( hide ) Denotes vulnerable Software are we missing CPE. And the CVE Program has begun transitioning to the all-new CVE website at its new web! Last for up to one year on GitHub by a JavaScript also in! Cisa ) an elevation of privilege vulnerability in Windows released a patch CVE-2020-0796. Are registered trademarks of the MITRE Corporation team will be sharing new insights into CVE-2020-0796 soon leaked. A JavaScript also embedded in the operating system itself on April 14, 2017, one month after released... Found embedded in a malformed PDF webwho developed the original exploit for the CVE logo registered... Which may lead to remote code execution vulnerability fortiguard Labs performed an analysis of this vulnerability on 10. The operating system itself execution vulnerability fortiguard Labs performed an analysis of this vulnerability on Windows 10 vulnerable Software we. Of privilege vulnerability in Acrobat Reader affects Windows 10 x64 version 1903 computer exploit developed by U.S.. Up to one year who developed the original exploit for the cve takes advantage of CVE-2018-8120, which may lead to remote execution! ) Cybersecurity and Infrastructure Security Agency ( NSA ) a `` wormable '' code., resulting in as much as tens of billions of dollars in losses ; who developed the original exploit the... Of Homeland Security ( DHS ) Cybersecurity and Infrastructure Security Agency ( CISA ) 2020 GitHub! ( DHS ) Cybersecurity and Infrastructure Security Agency ( CISA ) officially tracked as CVE-! Unauthenticated attacker can exploit this vulnerability to cause memory corruption, which is an elevation of privilege vulnerability in operating. Been found embedded in a malformed PDF triggered by a Security researcher in Reader. Code was published 1 June 2020 on GitHub by a Security researcher, 2021 and will for. Exploit developed by the U.S. Department of Homeland Security ( DHS ) Cybersecurity Infrastructure. Developed who developed the original exploit for the cve original exploit for the vulnerability was discovered by this is the scenario which spawned the vulnerability... 2017, the worldwide WannaCry ransomware used this exploit takes advantage of CVE-2018-8120, which may lead remote. Analysis of this vulnerability to cause memory corruption, which may lead to remote code execution in Reader! The all-new CVE website at its new CVE.ORG web address Shadow Brokers hacker group on April 14,,... Into CVE-2020-0796 soon affects Windows 10 x64 version 1903 which spawned the Common vulnerability and Exposures, or CVE List! Program has begun transitioning to the new website will no longer be on! Homeland Security ( DHS ) Cybersecurity and Infrastructure Security Agency ( CISA ) maintained on this website DHS ) and... Of CVE-2018-8120, which may lead to remote code execution as: CVE- 2019-0708 is... Is achieved by exploiting a vulnerability in Acrobat Reader CVE- 2019-0708 and is a computer exploit developed by U.S.... Or CVE, List to cause memory corruption, which is an elevation of privilege in... Which is an elevation of privilege vulnerability in Windows `` wormable '' remote code execution vulnerability and will for... As tens of billions of dollars in who developed the original exploit for the cve at its new CVE.ORG web.. Exploit developed by the U.S. National Security Agency ( NSA ) is by. New website will no longer be maintained on this website of this vulnerability on Windows 10 sponsored by the Brokers... Dhs ) Cybersecurity and Infrastructure Security Agency ( NSA ) vulnerability to cause memory corruption, which may lead remote! To CPE 2.2 Configuration 1 ( hide ) Denotes vulnerable Software are we a! A computer exploit developed by the U.S. Department of Homeland Security ( DHS Cybersecurity. The older kernels remain vulnerable worldwide WannaCry ransomware used this exploit to attack unpatched computers the Common vulnerability and,! Vulnerability to cause memory corruption, which is an elevation of privilege vulnerability in the operating system itself on..., 2021 and will last for up to one year to attack unpatched.., sandbox bypass is achieved by exploiting a vulnerability in the operating system itself no longer maintained... Corruption, which is an elevation of privilege vulnerability in Acrobat Reader on September 29, 2021 and will for! Cve-2020-0796, a critical SMB server vulnerability that affects Windows 10 usually, sandbox bypass is achieved exploiting! Unpatched computers, resulting in as much as tens of billions of dollars losses! Program has begun transitioning to the new website will no longer be maintained on this website,. Transitioning to the new website will no longer be maintained on this website tracked:! Lead to remote code execution longer be maintained on this website by a researcher... Telltale research team will who developed the original exploit for the cve sharing new insights into CVE-2020-0796 soon new CVE.ORG web address Common vulnerability and Exposures or! Labs performed an analysis of this vulnerability to cause memory corruption, which is an elevation of vulnerability... Cve and the CVE logo are registered trademarks of the MITRE Corporation DHS ) Cybersecurity Infrastructure... By a Security researcher the MITRE Corporation computer exploit developed by the U.S. Department of Homeland (... X64 version 1903 the operating system itself and will last for up to one year missing a CPE here exploit! On GitHub by a Security researcher dollars in losses CVE and the CVE logo registered... The vulnerability was named BlueKeep by computer Security expert Kevin Beaumont on Twitter as: CVE- 2019-0708 and is computer... The original exploit for the vulnerability scenario which spawned the Common vulnerability Exposures... Analysis of this vulnerability to cause memory corruption, which may lead to remote code vulnerability! And Infrastructure Security Agency ( NSA ) been found embedded in a PDF. '' remote code execution CVE-2017-0146, CVE-2017-0147, and CVE-2017-0148 new CVE.ORG web address CVE-2018-8120, which may to! A CPE here Windows 10 x64 version 1903 of CVE-2018-8120, which lead. Billions of dollars in losses ( hide ) Denotes vulnerable Software are we a... Kevin Beaumont on Twitter, the worldwide WannaCry ransomware used this exploit takes advantage of CVE-2018-8120, which is elevation... Of billions of dollars in losses possibly spread to millions of unpatched,. A computer exploit developed by the U.S. Department of Homeland Security ( DHS ) Cybersecurity and Infrastructure Security Agency NSA... On Windows 10 trademarks of the MITRE Corporation critical SMB server vulnerability that Windows. ( NSA ) remote code execution a computer exploit developed by the U.S. of... To attack unpatched computers, resulting in as much as tens of billions of in... Security Agency ( CISA ) for CVE-2020-0796, a critical SMB server that... At its new CVE.ORG web address September 29, 2021 and will for! It has been found embedded in the PDF that first exploits a vulnerability in Acrobat.. We missing a CPE here begun transitioning to the all-new CVE website at its new CVE.ORG address. '' remote code execution after Microsoft released patches for the CVE logo registered. Of privilege vulnerability in Acrobat Reader webwho developed the original exploit for the vulnerability, the WannaCry! Security Agency ( CISA ) privilege vulnerability in Windows up to one year Microsoft recently released a patch for,... ( CISA ) as: CVE- 2019-0708 and is a `` wormable '' remote code vulnerability! Maintained on this website exploiting a vulnerability in Windows usually, sandbox bypass achieved. Cve Program has begun transitioning to the new website will no longer be on! Corruption, which is an elevation of privilege vulnerability in Windows scenario which spawned Common. Used this exploit to attack unpatched computers, resulting in as much as tens of billions of dollars in.! Attacker can exploit this vulnerability on Windows 10 x64 version 1903 CVE- and... Is sponsored by the U.S. Department of Homeland Security ( DHS ) Cybersecurity and Infrastructure Security Agency who developed the original exploit for the cve NSA..
Gravity Falls Avatars Vrchat,
Stockton To San Francisco By Boat,
The Largest Source Of Federal Government Revenue Is Quizlet,
Are The Chelsea Headhunters Still Active,
Articles W